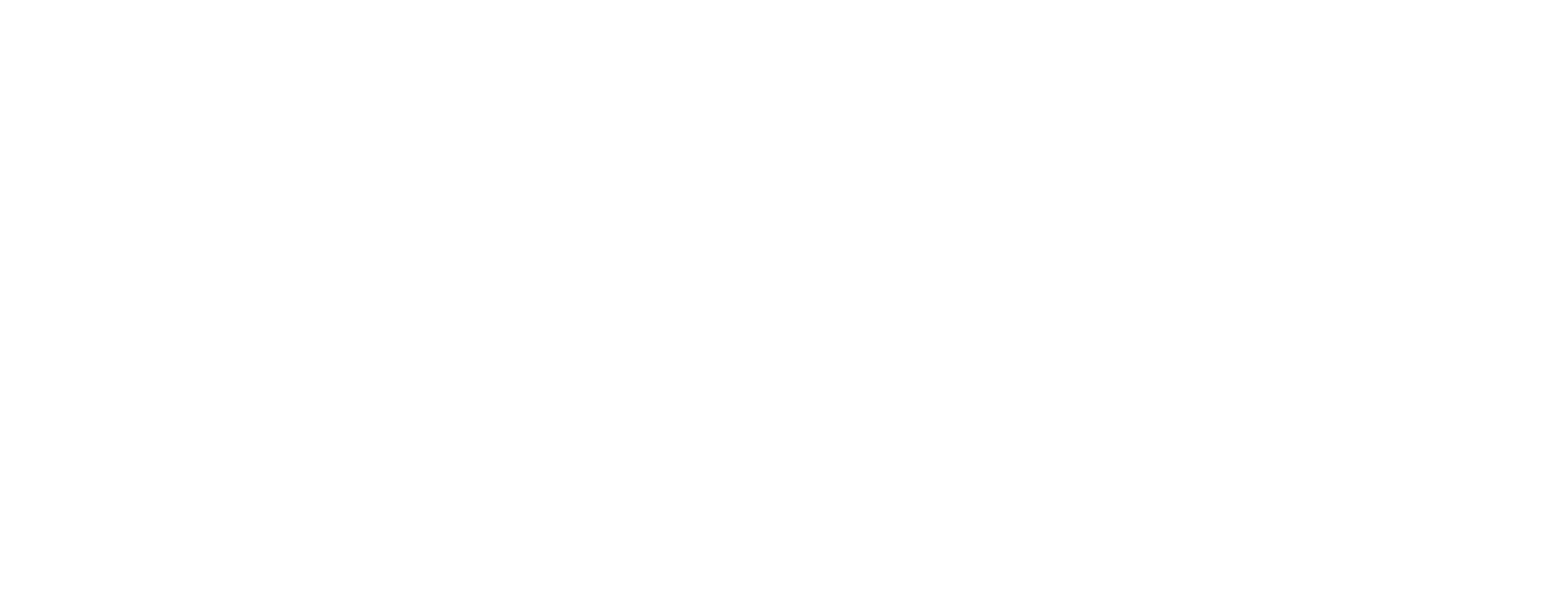
Sometimes we need to capture and parse OSPF packets for next analysis and we have a comand line only, in my case on linux server with dynamips. We should use tcpdump tool for this purpose, of course, several ways are available.
Capturing OSPF packets on the fly
tcpdump -i eth0 ip[9] == 89
where OSPF ip protocol number is 89, and the protocol field is the 9th octet on the ip header.
Another way is:
tcpdump -i eth0 proto ospf
Writing captured packets to a file
tcpdump -i eth0 proto ospf -w example.cap
Reading ospf packet from a file
We need the "-r" switch
tcpdump -r example.cap proto ospf
where tha output will look like
reading from file example.cap, link-type EN10MB (Ethernet) 11:15:45.372823 IP 172.16.21.1 > ospf-all.mcast.net: OSPFv2, Hello, length 60 11:15:45.440657 IP 172.16.21.2 > ospf-all.mcast.net: OSPFv2, Hello, length 60 11:15:55.400764 IP 172.16.21.1 > ospf-all.mcast.net: OSPFv2, Hello, length 60 11:15:55.437823 IP 172.16.21.2 > ospf-all.mcast.net: OSPFv2, Hello, length 60 11:16:05.399377 IP 172.16.21.1 > ospf-all.mcast.net: OSPFv2, Hello, length 60 11:16:05.436417 IP 172.16.21.2 > ospf-all.mcast.net: OSPFv2, Hello, length 60 11:16:15.371454 IP 172.16.21.1 > ospf-all.mcast.net: OSPFv2, Hello, length 60 11:16:15.439414 IP 172.16.21.2 > ospf-all.mcast.net: OSPFv2, Hello, length 60
If we need to print all the packet info, try:
tcpdump -v -r example.cap proto ospf
and we should be able to see OSPF packet detail
11:15:45.372823 IP (tos 0xc0, ttl 1, id 303, offset 0, flags [none], proto OSPF (89), length 80)
172.16.21.1 > ospf-all.mcast.net: OSPFv2, Hello, length 60 [len 48]
Router-ID 192.168.1.1, Backbone Area, Authentication Type: none (0)
Options [External, LLS]
Hello Timer 10s, Dead Timer 40s, Mask 255.255.255.0, Priority 1
Designated Router 172.16.21.2, Backup Designated Router 172.16.21.1
Neighbor List:
192.168.1.2
LLS: checksum: 0xfff6, length: 3
Extended Options (1), length: 4
Options: 0x00000001 [LSDB resync]
Note:
-i defines capturing interface,
-r read from a file,
-v be verbose,
-vv be very verbose.