Author: Tomas Misutka
This article provides a how-to guide on how to add/join a Linux-based system (server, workstation) to a Windows domain working with Active Directory.
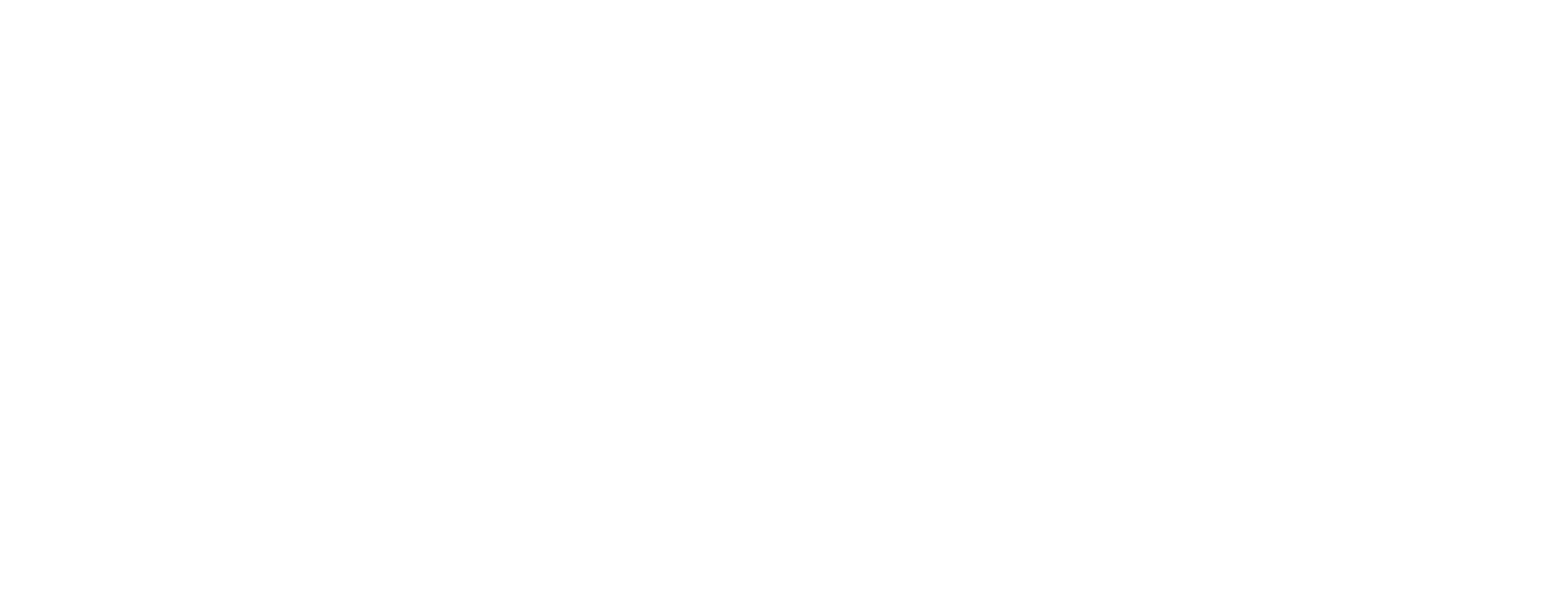
This tutorial was tested on machines:
- DEBIAN -> version:8.11.1 SSSD version:1.11.7-3+deb8u2
- UBUNTU-SERVER -> version:20.04 SSSD version:2.2.3-3 ]
- Win server 2016
- For demonstrtation purposes as the configuration of KERBEROS we use Win domain named WIN.KIS.FRI.UNIZA.SK – default realm
Join to a domain follow steps.
sudo apt-get update
Install required packages
sudo apt-get install krb5-user sssd ntp ntpdate realmd
Back up default kerberos file
sudo mv /etc/krb5.conf /etc/krb5.conf.default
Create a new kerberos file
sudo nano /etc/krb5.conf
and insert lines
[libdefaults]
default_realm = WIN.KIS.FRI.UNIZA.SK
rdns = no
dns_lookup_kdc = true
dns_lookup_realm = true
[realms]
WIN.KIS.FRI.UNIZA.SK = {
kdc = dc.kis.fri.uniza.sk
admin_server = dc.kis.fri.uniza.sk
}
then generate kerberos ticket using the admin or any other admin’s account
kinit administrator
show generated ticket
klist --verbose
check, if a domain is available
realm discover win.kis.fri.uniza.sk --verbose
join machine to domain, use administrator’s account or any other admin’s account
realm join --user=administrator@WIN.KIS.FRI.UNIZA.SK WIN.KIS.FRI.UNIZA.SK --verbose
show domain information
realm list (--verbose DOESN'T SHOW MORE INFO)
and make sure, that the computer is added on dc in computer container (refresh) .
Than make sure, that file in /etc/sssd/sssd.conf has permission to 0600
ls -l /etc/sssd/sssd.conf
if not, change that
chmod 0600 /etc/sssd/sssd.conf
edit sssd.conf file and insert
[sssd] services = nss, pam, ssh config_file_version = 2 domains = win.kis.fri.uniza.sk [nss] entry_negative_timeout = 0 reconnection_retries = 3 entry_cache_timeout = 300 entry_cache_nowait_percentage = 75 [pam] reconnection_retries = 3 offline_credentials_expiration = 2 offline_failed_login_attempts = 3 offline_failed_login_delay = 5 debug_level = 9 [ssh] [domain/win.kis.fri.uniza.sk] enumerate = false id_provider = ad auth_provider = ad chpass_provider = ad access_provider = ad dyndns_update = false ad_hostname = debian-test.win.kis.fri.uniza.sk ad_server = dc.kis.fri.uniza.sk ad_domain = win.kis.fri.uniza.sk ldap_schema = ad ldap_id_mapping = true fallback_homedir = /home/%d/%u default_shell = /bin/bash ldap_sasl_mech = gssapi ldap_sasl_authid = DEBIAN-TEST krb5_store_password_if_offline = true ldap_krb5_init_creds = true cache_credentials = true realmd_tags = manages-system joined-with-adcli
save it and restart SSSD
systemctl restart sssd
and add line to common-session file to create a new home directory while first login
sudo nano /etc/pam.d/common-session
find line with „session required pam_unix.so“ and paste below
session required pam_mkhomedir.so skel=/etc/skel umask=0077
save it and add admins group to sudoers file
visudo %name_of_group ALL=(ALL:ALL) ALL //prefered
or
%name_of_group@domain ALL=(ALL:ALL) ALL
if a group includes space, use this format
%first_name\ second_name ALL=(ALL:ALL) ALL
done! Reboot computer and enjoy