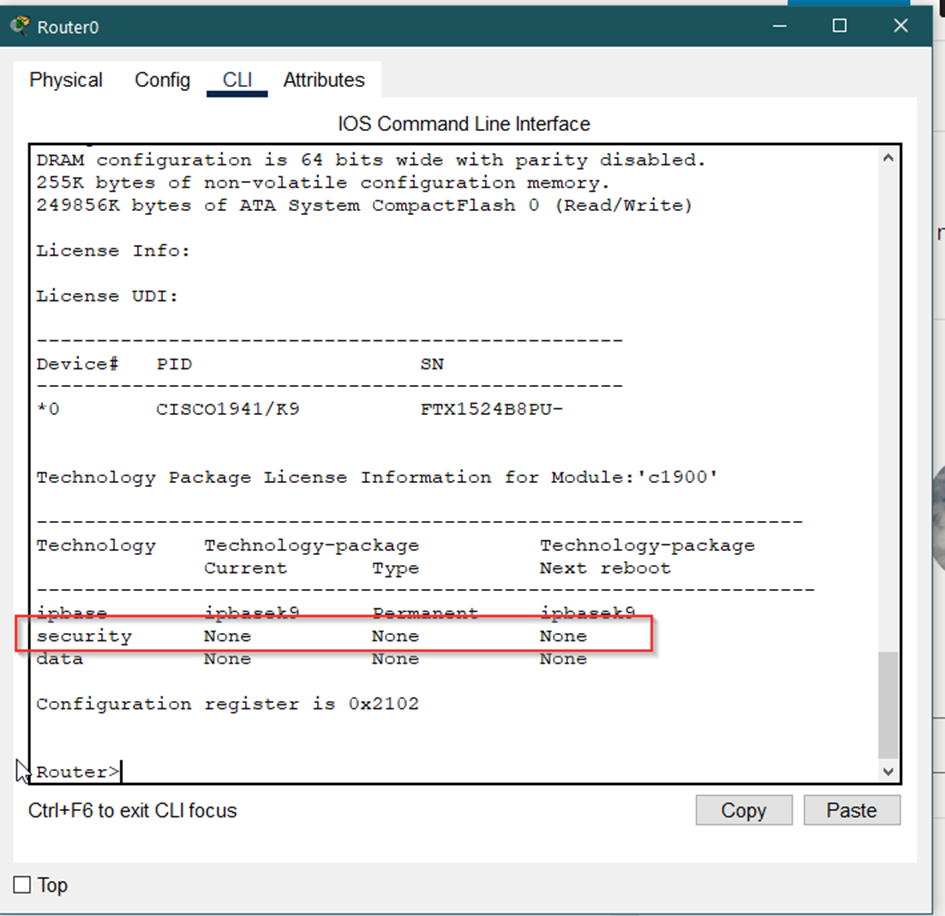
The article describes configuration of the AAA service on Cisco ASA against a Network policy server running on Windows 2016 server. The implementation of Network policy server on Windows is de-facto Microsoft implementation of RADIUS server.
Configuration of AAA radius server on Cisco ASA
ASDM
1) Connect to your ASA using ASDM
2) From the menu select „Configuration“
3) From the left panel select „Remote Access VPN“
4) Within of the „Remote Access VPN“ select AAA/Local Users
5) Then select „AAA Server Group“
6) On the right two panels appears, the „AAA Server Group“ and the „Servers in the Selected Group“
7) Add a new server within the Server Group
– choose the name for the server group
– select RADIUS as the protocol
– other options we may leave default
8) Now choose just created server group and within of the second half of panel (the bottom one) add the new server
– select the ASA interface where the server will operate
– specify the IP address of the server
– specify the „Server Secret Key“
– check the „MS CHAPv2 Capable“ option
9) Ok and APPLY
Command line
The configuration in general is:
aaa-server NAME protocol radius aaa-server NAME (INTERFACE) host IP_ADDRESS key *****
aaa-server KIS-DC protocol radius aaa-server KIS-DC (vlan200) host 192.168.200.2 key *****
Configuration of Windows 2016 Server – configuration of the Network police server
1) Login to your windows server
2) Open „Server Manager“
3) From the Dashboard select „Add roles and features“ (or through Manage > Add roles and features)
4) Go through welcome page selecting Next
5) Select „Role-based or feature-based installation“ and go Next
6) Select your server then Next
7) We are on the „Server roles“ step, where we select „Network Policy and Access Services“, then click Next
8) Click „Add features“ and then Next/Next and finally Install
9) Once the installation finish click Close
10) Then from the „Server Manager“ select „NPAS“
11) In SERVERS panel right click on just installed server and select „Network Policy Server“
12) Right click on NPS (Local) and select „Register server in Active Directory“
13) From the Left menu expand „RADIUS Clients and Servers“
14) Right click on the RADIUS Client and select „New“
15) Setup a new radius client, which means:
– Check „Enable this RADIUS client“
– in „Friendly name“ specify the name for an ASA client, in my case (for example) „cisco-asa“
– In „Address“ specify th eIP address of your ASA box or its DNS name (if it is configured)
– select „Manual“ at the bottom and specify Shared secret (the one previously configured previously on the ASA box)
– Confirm secret
– Click OK
16) then expand Policies and do the right click on „Connection Request Policies“ where select „New“
17) Specify the name within the Policy Name
18) In „Specify condition“ add a condition, where select „Client Friendly Name“‚ and click Add
19) Specify the name for the condition, for example the same as was done above (cisco-asa)
20) Then Next/Next and after „Specify Authentication Methods“ step within „Configure Settings“ select the „User-Name“ attribute and Finish
21) Now right click on the Network Policies and select New
22) Specify the name within the „Policy-name“ form and go Next
23) then Specify conditions where we need to select „User Groups“
24) Add users group which we wish to allows access. The list is taken from the active directory server, I selected for example Domain Users, then click Next
25) Select Access granted and go Next
26) Select „Unencrypted Authentication PAP SPAP“ and go Next.
27) Then select No when asking for Connection Request Policy and go Next
28) Go Next and finish
Testing
Test the authentication. We may use for it the ASA ASDM, where on the same page as we have added servers there is the Test button where we may specify the name and password ad check if the authentication was successful.






skuska
Good article, but needs language review.
thx, some coorections done